Secure remote access solutions are worthy assets to your organization, helping you to:
- Keep sensitive data secure. Protect your organization’s data by limiting access from outside sources and only granting it by a secure, controlled means. ...
- Reduce the attack surface. ...
- Achieve and maintain compliance. ...
What is secure remote access and how does it work?
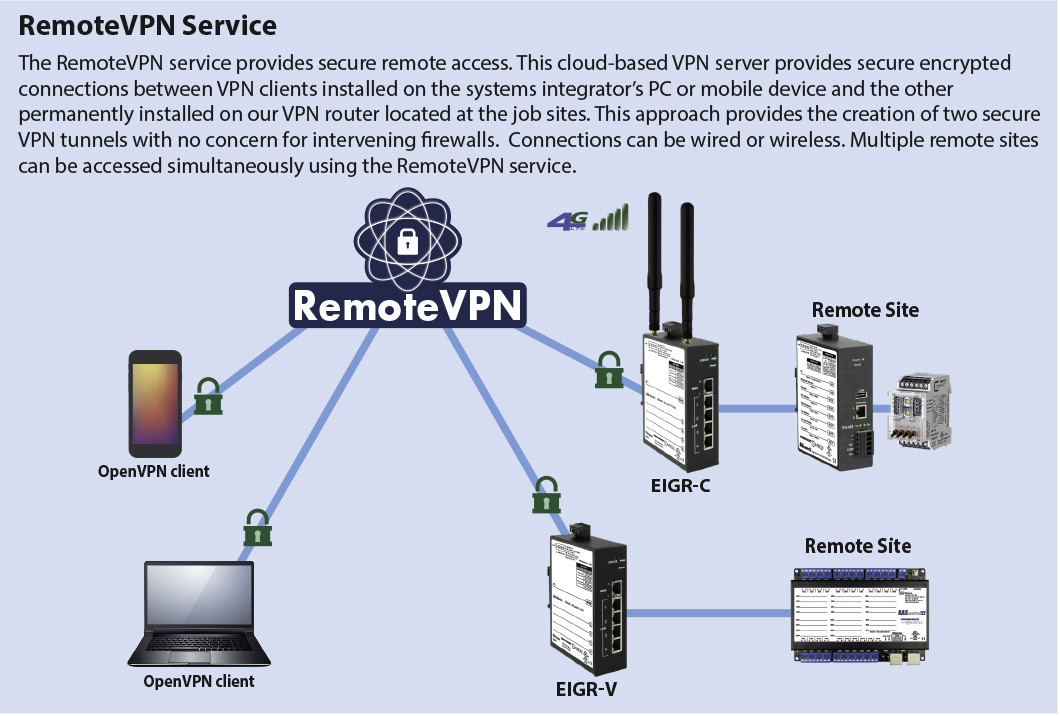
Secure remote access refers to any security policy, solution, strategy or process that exists to prevent unauthorized access to your network, its resources, or any confidential or sensitive data. Essentially, secure remote access is a mix of security strategies and not necessarily one specific technology like a VPN.
How to choose the best secure remote access solutions?
The best secure remote access solutions should include robust endpoint management to help organizations protect employee endpoints like laptops, smartphones, tablets and IoT devices.
What is remote access software?
What Is Remote Access Software? Remote access software lets one computer view or control another computer, not merely across a network, but from anywhere in the world.
What are the advantages of remote access?
What is remote computer access? 1 The ability to troubleshoot quickly. 2 Easy monitoring and control of devices connected to the same network. 3 Efficient file-sharing. 4 The ability of your device to mirror the original device, including files and applications.
Is remote access security secure?
Yes. A robust cloud-based, highly secure remote access solution can provide unified protection for virtually all users against web-based threats — independent of a VPN connection.
Can remote access be hacked?
Remote desktop hacks become a common way for hackers to access valuable password and system information on networks that rely on RDP to function. Malicious actors are constantly developing more and more creative ways to access private data and secure information that they can use as leverage for ransom payments.
What are the risks of remote access?
Many remote access security risks abound, but below is a list of the ones that jump out.Lack of information. ... Password sharing. ... Software. ... Personal devices. ... Patching. ... Vulnerable backups. ... Device hygiene. ... Phishing attacks.
Which method of remote access is the most secure?
Implement a Secure Connection for Remote Network AccessWired Connection: A wired connection is the most secure method for remote network access.Home Wi-Fi: The second most secure network connection is using a secured home Wi-Fi connection.More items...•
What happens if you give someone remote access to your computer?
This can be even worse than just conning you out of money, as undetected malware can allow hackers to steal your identity, including your passwords and financial information, over and over again, even if you get new passwords and account numbers.
Can my company see my Remote Desktop?
Can my employer see me at home via Citrix, Terminal, and Remote Desktop sessions? A: NO, your employer cannot see you at home through the Citrix/Terminal Server or Remote Desktop sessions. The way this technology works, it is not possible in general.
Can someone remotely access my computer without my knowledge?
"Can someone access my computer remotely without me knowing?" The answer is "Yes!". This could happen when you are connected to the internet on your device.
Is Google remote access secure?
Is Chrome Remote Desktop secure? While there is always some inherent risk involved with remote desktop software, Chrome Remote Desktop is secure and safe. All remote sessions are AES encrypted over a secure SSL connection, which means your data is protected while you remotely access your computer.
How do you protect remote access?
Basic Security Tips for Remote DesktopUse strong passwords. ... Use Two-factor authentication. ... Update your software. ... Restrict access using firewalls. ... Enable Network Level Authentication. ... Limit users who can log in using Remote Desktop. ... Set an account lockout policy.
How do I create a secure remote access?
7 Best Practices For Securing Remote Access for EmployeesDevelop a Cybersecurity Policy For Remote Workers. ... Choose a Remote Access Software. ... Use Encryption. ... Implement a Password Management Software. ... Apply Two-factor Authentication. ... Employ the Principle of Least Privilege. ... Create Employee Cybersecurity Training.
How do I secure remote access to my network?
Use virtual private networks (VPN) - Many remote users will want to connect from insecure Wi-Fi or other untrusted network connections. VPNs can eliminate that risk, however VPN endpoint software must also be kept up-to-date to avoid vulnerabilities that can occur from older versions of the software client.
How do hackers hack remotely?
Remote hackers use various malware deployment methods; the most common (and probably the easiest) way for hackers to reach unsuspecting victims is through phishing campaigns. In this scenario, hackers will send emails with links or files, which unsuspecting recipients may click on.
Can someone access my computer without me knowing?
There are two ways someone can access your computer without your consent. Either a family member or work college is physically logging in to your computer or phone when you are not around, or someone is accessing your computer remotely.
How do I trace remote access?
1:132:22How to trace remote access logs VPN access - YouTubeYouTubeStart of suggested clipEnd of suggested clipAnd I'm just gonna type in C colon backslash Windows backslash tracing and that's gonna open up myMoreAnd I'm just gonna type in C colon backslash Windows backslash tracing and that's gonna open up my tracing directory.
What remote access methods could an attacker exploit?
Common remote access attacks An attacker could breach a system via remote access by: Scanning the Internet for vulnerable IP addresses. Running a password-cracking tool. Simulating a remote access session with cracked username and password information.
Why are IPs never exposed to the internet?
IPs are never exposed to the internet, creating a “darknet” and making the network impossible to find. Apps segmentation ensures that once users are authorized, application access is granted on a one-to-one basis so that authorized users have access only to specific applications rather than full access to the network.
Can IoT services be hosted on premises?
IoT services that are hosted on-premises can benefit from optimized speeds. Performance speeds can increase if local users do not have to connect out to the internet to access apps that are hosted on-premises. The other option is ZTNA as a service, such as Zscaler Private Access.
Can a VPN be found by adversaries?
Opening the network in this way enables it to be “found” by your remote users, but it also means it can be found by adversaries. They can (and do) exploit the VPN attack surface to infiltrate the network, deliver malware such as ransomware, launch denial-of-service attacks, and exfiltrate critical business data.
What is secure remote access?
Secure remote access refers to any security policy, solution, strategy or process that exists to prevent unauthorized access to your network, its resources, or any confidential or sensitive data. Essentially, secure remote access is a mix of security strategies and not necessarily one specific technology like a VPN.
What technologies are used for secure remote access?
Secure remote access is comprised of a multitude of security solutions and technologies. Some of the most prominent include the following:
Secure remote access solution
Enables employees with precise access to the applications and data required to do their job from anywhere.
Why is secure remote access important?
With the work from home shift in the workforce, endpoints are accessing corporate networks from multiple locations. Today, employees’ home networks are often the originating point for network connections, multiplying the risk on both home and corporate networks.
What are the benefits of secure remote access?
While the benefits of secure remote access are numerous, there are four key advantages in which to focus on:
Can secure remote access be achieved without VPN?
Yes. A robust cloud-based, highly secure remote access solution can provide unified protection for virtually all users against web-based threats — independent of a VPN connection.
How can AT&T help organizations with secure remote access?
AT&T Cybersecurity is uniquely positioned to help organizations address these immediate challenges with an eye toward the future by helping them balance connectivity, collaboration, and cybersecurity affordably.
How does secure remote access work?
Enabling remote access means walking a tightrope between usability and cybersecurity. Every remote worker needs a way to connect with remote desktop services and applications that won't slow down their workflows. At the same time, IT administrators must manage those connections to ensure they don't leave the network open to threats.
Why is secure remote access important to remote work security?
Secure remote access approaches are so vital because it’s now impossible to control security at the endpoint. Each user in a remote or hybrid workforce is connecting to the network from a different type of computer or smartphone, and they’re using a variety of internet connections to log in.
What are the options for secure remote access?
Multiple solutions go into a comprehensive secure remote access package—and each one delivers vital functionality that reflects the way companies use their networks today. These features work together to protect users, data, and network assets in a distinct way.
Next-gen remote access solutions for a secure digital workspace
Learn how remote access solutions can secure digital workspaces and enhance the user experience.
Citrix solutions for secure remote access
Citrix secure access solutions take several forms to give companies a balanced selection of options based on their specific requirements. Whatever level of engagement with remote work these businesses have, there is a secure remote access solution for the situation.
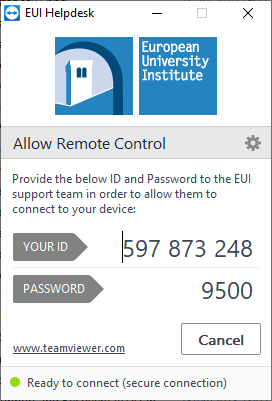
What does it mean when someone gives you remote access to your computer?
When you grant somebody remote access to your computer, in effect, you are physically handing over your machine to them - the person will be able to do almost anything with your system. This fact is quite concerning, especially if there’s a hacker on the other side.
What is remote desktop?
A remote desktop is a computer which you connect to from your local computer, so the device you’re using.
How do scammers gain access to your computer?
Scammers usually use social engineering tactics to gain access to your computer. They will pretend to be from a large telecommunication company, convincing you your computer needs an urgent fix via a remote connection. When you grant access, they can install malware or ransomware to breach your security or demand payment for the repair.
Is remote access a double edged sword?
Remote access is a double-edged sword: it can either save you time and effort or potentially expose your computer to infection from malware. Let’s dive deeper into the topic to understand the possible risks and learn the best ways to protect yourself.
Is it safe to use a remote desktop?
The remote connection itself is quite safe: Windows and macOS have inbuilt remote desktop clients allowing remote connection between computers. Security concerns are more a matter of who accesses your computer and what they are doing there.
Why is remote access important?
Remote access software is helpful when you’re in a meeting at another office with your laptop — or telecommuting — and need an important file that’s on your office computer. Remote computer access can help you assist someone in your personal life who might be far away.
How to protect your computer when using remote access?
Here are some steps you can take to help protect your computer and data while relying on remote access. Maintain strong passwords.
Is there a third party remote access program?
For instance, there are Windows-only and Mac-only programs if your computers and devices all use the same operating system.
Can hackers use RDP?
Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular. Remote desktop servers connect directly to the Internet when you forward ports on your router. Hackers and malware may be able to attack a weakness in those routers.
What is secure remote access?
What it means to provide secure remote access has changed considerably in the past few years as a result of new technologies and the pandemic. At its most basic, secure remote access is having location-agnostic connectivity among enterprise users and centralized applications, resources and systems, whether cloud-based or on premises.
Who is responsible for secure remote access?
Although remote access tools, such as VPNs and firewalls, are typically under the purview of network teams, in this new era, cybersecurity teams tend to lead and manage the policies, processes and technologies associated with ensuring secure remote access.
The diminishing power of VPNs
One tactic organizations use to combat the vulnerabilities associated with working remotely -- especially if employees are using consumer-grade systems -- is to reestablish VPN standards. This entails enforcing basic protections, such as strong passwords, multifactor authentication, role-based access and encryption.
Setting secure remote access policies
A hallmark of secure remote access is the underlying policy that safeguards access to and the use of enterprise resources, such as data, databases, systems and networks.
Components of the secure remote access ecosystem
Secure remote access touches just about every aspect of enterprise security. TechTarget has curated a series of guides to help IT and security professionals get up to speed on important technologies and concepts.
Zero trust and secure remote access
Cybersecurity and IT teams realize words like perimeter and trust are quickly becoming outdated as borders dissolve and the base of users that need access to resources expands. No longer are organizations protected by four castle walls, with a firewall moat keeping miscreants out.
SASE and secure remote access
Secure Access Service Edge is an emerging concept that combines network and security functions into a single cloud service, not only to alleviate traffic from being routed through the data center, but also to embrace a remote workforce, IoT adoption and cloud-based application use.
What is remote access app?
Remote access apps let you either access your home or office computer from another location, or allow others to have access to some or all of your files, as if they were actually sitting in front of your PC instead of somewhere else entirely.
Is VNC Connect secure?
VNC Connect is solid, secure, and simple to use, once you get the hang of it. It has fewer features than other corporate-level remote access software, but it's also a lot less expensive.