
Hackers use Common remote access tools to penetrate third-party access to merchant information without physically being on the location. Although these same tools also allow employees to access work systems from remote locations - a common practice in today's mobile world.
Full Answer
How to stop remote hacking?
- Educate your employees. Like most things in life, it all begins with education. ...
- Make VPNs mandatory. A virtual private network, or VPN, establishes a protected connection even when you’re using a public network.
- Use shared documents. ...
- Implement two-factor authentication. ...
- Teach staff how to recognise hacking attempts. ...
- Enforce regular password changes. ...
How to block remote hackers?
Steps
- Follow forums. It is always a good idea to follow hacking forums as you will be able to pick up on all the latest methods being used.
- Change default passwords immediately. Some software has built-in passwords to allow the first login after installation; it is extremely unwise to leave it unchanged.
- Identify entry points. ...
How can I prevent remote access to my Windows PC?
Windows 8 and 7 Instructions
- Click the Start button and then Control Panel.
- Open System and Security.
- Choose System in the right panel.
- Select Remote Settings from the left pane to open the System Properties dialog box for the Remote tab.
- Click Don’t Allow Connections to This Computer and then click OK.
What is the best remote access for PC?
What is the Best Remote Desktop Software?
- GoToMyPC. GoToMyPC is the best remote desktop software on this list. ...
- AnyDesk. AnyDesk is one of the most popular remote desktop software platforms, used by over 100 million users globally.
- LogMeIn. ...
- Parallels. ...
- Splashtop Business Access. ...
- Zoho Assist. ...
- ConnectWise Control. ...
- RemotePC. ...
- TeamViewer. ...
- Remote Utilities for Windows. ...
Do hackers use remote access?
Remote Desktop Protocol (RDP) has been known since 2016 as a way to attack some computers and networks. Malicious cyber actors, hackers, have developed methods of identifying and exploiting vulnerable RDP sessions via the Internet to steal identities, login credentials and install and launch ransomeware attacks.
How do hackers use remote desktop?
Hackers use RDP to gain access to the host computer or network and then install ransomware on the system. Once installed, regular users lose access to their devices, data, and the larger network until payment is made.
What remote access software do hackers use?
3) RAT (Remote Access Trojan) Remote hackers use various malware deployment methods; the most common (and probably the easiest) way for hackers to reach unsuspecting victims is through phishing campaigns.
What is a remote hack?
A remote attack refers to a malicious attack that targets one or more computers on a network. Remote hackers look for vulnerable points in a network's security to remotely compromise systems, steal data, and cause many other kinds of problems.
Can someone remotely access your computer?
Hackers could use remote desktop protocol (RDP) to remotely access Windows computers in particular. Remote desktop servers connect directly to the Internet when you forward ports on your router. Hackers and malware may be able to attack a weakness in those routers.
Why do spammers use RDP?
RDP access gives an attacker full control over a remote PC with almost no limitations. That makes RDP access an attractive target for hackers. Hacked RDP servers can be found for sale in the thousands on hacker forums and marketplaces.
Can hackers use TeamViewer?
The FBI alert doesn't specifically tell organizations to uninstall TeamViewer or any other type of desktop sharing software but warns that TeamViewer and other similar software can be abused if attackers gain access to employee account credentials or if remote access accounts (such as those used for Windows RDP access) ...
Can I be hacked with AnyDesk?
AnyDesk was abused by individuals to steal from users who did not understand the need to keep their access codes as safe as they do their personal data. AnyDesk is an exceptionally secure software for remote connections, using banking-level security and encryption protocols.
Can someone access my phone remotely?
Some spy apps are pretty easy to get hold of and can be used by a person without advanced IT knowledge. This lets them remotely monitor your phone activities. A person can install such an app by getting a direct access to your mobile device; A USB cable or charger lead could be used to hack your device.
What are remote access attacks?
A remote attack is a malicious action that targets one or a network of computers. The remote attack does not affect the computer the attacker is using. Instead, the attacker will find vulnerable points in a computer or network's security software to access the machine or system.
Can hackers control your phone?
Skilled hackers can take over a hacked smartphone and do everything from making overseas phone calls, sending texts, and using your phone's browser to shop on the Internet. Since they're not paying your smartphone bill, they don't care about exceeding your data limits.
How do hackers get access to your computer?
Access to a corporate or public wifi network allows hackers to carry out various operations such as sniffing users' credentials, executing a man-in-the-middle attack, and even redirecting victims to malicious websites for further compromise. People often associate computer hacking with compromising a system remotely.
What is RDP in cyber security?
Remote Desktop Protocol (RDP) is a Microsoft proprietary protocol that enables remote connections to other computers, typically over TCP port 3389. It provides network access for a remote user over an encrypted channel.
How can Hackers Exploit Remote Access Software?
Hackers have several ways of exploiting the vulnerabilities of remote access software in hopes of causing a security incident to a private network or system. If there’s a poor protocol for installing remote access software, then there’s a high chance for hackers to gain unwanted access to your system.
Why is it important to secure remote access?
By securing remote access software, you’ll be able to have a safe environment away from security threats and risks that come with the utilization of remote access.
What is Remote Access Software?
Remote access software is a type of program that allows a computer to be accessed and control remotely while its screen is being displayed on a client’s computing device. Most of today’s businesses use this technology to effectively manage business operations in and out of the country, conduct remote meetings and conferences, and allow employees to access their files even outside of a corporate space. For small businesses, remote access software acts as a tool that allows them to outsource IT services and maintenance.
How do cybercriminals attack?
It’s a common practice for cybercriminals to launch attacks by tricking people through phishing scams and deceitful malware-mounted files. Hackers may also exploit the vulnerabilities of a private network or a system to steal confidential information and data. Though these types of malicious practices have become a norm in the field of modern hacking and online theft, another exploitable technology has also become a desirable prey for modern hackers – remote access software.
Why do you need to use two factor authentication?
Using two-factor authentication can help you strengthen your passwords even more. By combining two user identifications, hackers may have a difficult time decoding your passwords and breaking into your private system. You can also use unique passwords for each remote access account to ensure that security of your system against cybercriminals and hackers.
How did Russian hackers get into European embassies?
An article released by Sify Finance revealed that a group of Russian hackers were able to target a number of European embassies by using popular remote access software. These hackers sent out deceitful files that they disguised as a credible US government data to the targeted embassies in Kenya, Liberia, Nepal, Guyana, Italy, Bermuda, Lebanon, and others. Once viewed, these hackers were able to gain access to the targeted computer by unwillingly installing the said remote access software.
Why is it important to strengthen passwords?
That’s why it’s necessary for businesses to strengthen their account codes to ensure that they have strong initial security against cyber criminals and hackers. Using remote access software outside of a local network can also enable hackers to execute brute force attacks by trying to decode weak passwords and codes. Once they gain access to your system, they’ll be able to acquire information that can result in a major security incident.
What are remote hackers?
With the rise of a remote working population, “remote hackers” have been re-emerging as well. These remote hackers take advantage of remote working technologies like video conferencing tools, enterprise VPNs, and other remote access solutions that have become popular during the COVID-19 crisis.
How do remote hackers reach unsuspecting victims?
Remote hackers use various malware deployment methods; the most common (and probably the easiest) way for hackers to reach unsuspecting victims is through phishing campaigns.
What are hackers exploiting?
While hackers are exploiting the vulnerabilities found in actual solutions like business VPNs and RDP to gain access to the company network, they are using traditional tactics to target remote employees.
Why do VPNs run 24/7?
VPNs run 24/7, which means organizations are less likely to check for and apply security patches on a regular basis. This also makes VPNs vulnerable and susceptible to attacks by hackers. For instance, hackers may start a phishing campaign to target remote employees in order to steal their usernames and passwords that gives them access to the VPN, and by extension, your network.
Why are automated bots important?
In the wake of the coronavirus outbreak, companies in industries like healthcare are tapping into the power of automated bots to help identify vulnerable patients and screen employees. While bots have their evident merits, hackers can also harness the power of automated bots for malicious purposes.
What is the 2015 breach of the human resources department?
The 2015 data breach of the human resources department for the US federal government is a prime example of hackers exploiting internal data through a weak VPN.
Why are video conferencing tools vulnerable?
Video conferencing tools remain vulnerable because virtual meetings sometimes only require an invitation link and ID, but not a password. Users may also be too lazy to update security patches to the latest version, which can make using these tools vulnerable to unwanted intrusions.
How Do Hackers Gain Access?
There are several ways hackers can gain access to a network remotely using this software: lack of governance for installing remote access software and weak remote access account passwords. If a company’s employees are unaware that they’ve installed remote access software on company devices, then there is potential for abuse as it increases the risk of hackers finding a backdoor.
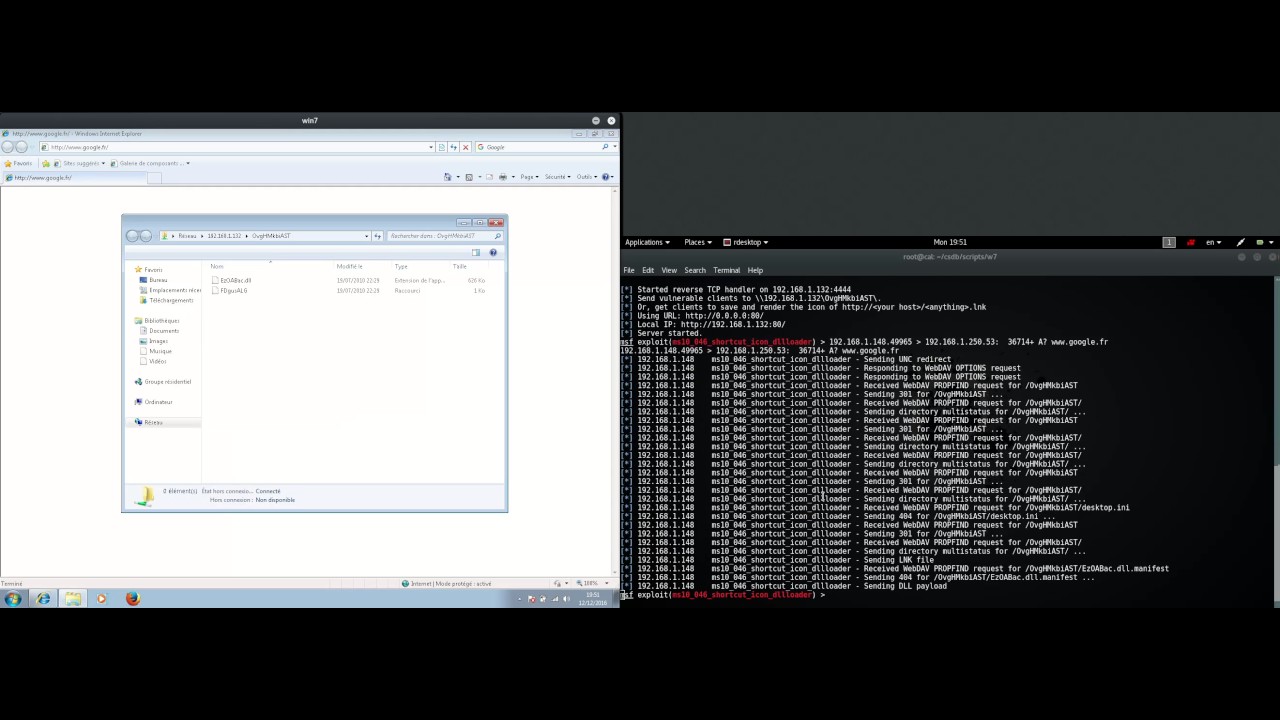
What is RDP hacking?
Hackers are getting more and more creative in their hacking methods, and using the RDP is one way they can make their way into a company’s network. In fact, Naked Security recently reported on a growing trend of hackers spreading ransomware by accessing computer systems through the RDP.
Why is it important to choose a strong password for remote access?
It’s extremely important for businesses to choose a strong password for their remote access accounts. If the RDP is exposed to the Internet, a simple network engine can allow hackers to poke around the network and use various methods like brute force attacks to try and guess the password. Once inside the system, it’s only a matter of time before they acquire access information needed to infiltrate other critical systems.
What is fileless attack?
Previously, we discussed fileless attacks, an increasingly popular method used by hackers to spread ransomware that sometimes involves exploiting the macro functionality in Microsoft Office documents. Now, it appears that another exploitable entry point has been on the rise: remote access software.
Why were the WannaCry and NotPetya attacks successful?
Both the WannaCry and NotPetya attacks, for example, were successful because hackers used leaked NSA exploits to infect older computer operating systems.
How do hackers sneak into a network?
Hackers typically sneak remotely into the networks of their victims by setting up phishing scams and duping users into downloading malware-ridden files, which are then executed to commence a cyberattack like ransomware. They may also look for vulnerabilities in computer systems to attempt to get into a network.
Why do hackers install low level software?
Hackers are able to secretly download and install low-level system tweaking software into a company’s server to disable anti-malware protections and lay the ground for a larger attack.
How to protect remote desktop from hackers?
Use a secure Virtual Private Network (VPN). If you set up a VPN, your remote desktop server won’t be connected directly to the internet. It will only be exposed on your local network, which could leave it less vulnerable to hackers.
How to protect your network from remote access?
You should set up firewalls to restrict access using software or hardware or both.
What is remote computer access?
Many people take their laptops with them to do things like finish a business presentation while waiting for a flight at the airport. But a lot of those laptops may not have bigger, important files on them. You might leave those files at work or at home on your desktop computer.
What is remote access software?
Remote computer access software lets you access networks and computers remotely. It can enable file sharing. It’s like having a remote control for a computer or system that isn’t near you. You’ll be able to remotely download files and applications from your desktop or another person’s computer onto your laptop or your cell phone. Remote access also gives you control over that remote device
Why is it important to limit the number of users who can log in?
Remote computer access can help businesses, individuals, and families in a variety of ways. But it’s important to make remote access secure .
How to protect your computer when using remote access?
Here are some steps you can take to help protect your computer and data while relying on remote access. Maintain strong passwords.
Why is it important to lock your computer?
Set up an account lockout policy. To help guard against hackers implementing brute-force attacks with automated password-guessing tools, it’s important to set your computer to lock your accounts when someone enters an incorrect password a set number of times.
How to stop someone from accessing my computer?
This includes removing any Ethernet cables and turning off your Wi-Fi connections.
How to install antivirus on another computer?
If you don't have an antivirus, download an installer on another computer and transfer it to your computer via USB. Install the antivirus and then run a scan with it.
How to know if malware has been removed?
Monitor your computer after removing any malware. If your antivirus and/or Anti-Malware found malicious programs, you may have successfully removed the infection, but you'll need to keep a close eye on your computer to ensure that the infection hasn't remained hidden.
What to do if your computer is compromised?
Change all of your passwords . If your computer was compromised, then there’s a possibility that all of your passwords have been recorded with a keylogger. If you’re sure the infection is gone, change the passwords for all of your various accounts. You should avoid using the same password for multiple services.
Why is public Wi-Fi so dangerous?
Try to avoid public Wi-Fi spots. Public Wi-Fi spots are risky because you have zero control over the network. You can't know if someone else using the spot is monitoring traffic to and from your computer. By doing this, they could gain access to your open browser session or worse. You can mitigate this risk by using a VPN whenever you are connected to a public Wi-Fi spot, which will encrypt your transfers.
How to get rid of rootkits?
Download and run the Malwarebyte s Anti-Rootkit Beta. You can get this program for free from https://www.malwarebytes.com/antirootkit. This will detect and remove "rootkits," which are malicious programs that exist deep in your system files. The program will scan your computer, which may take a while to complete.
Can a computer be remotely accessed?
The chances of your specific computer being remotely accessed, while not impossible, are very low. You can take steps to help prevent intrusions.
How do hackers gain access to a network?
Hackers gain access to a network by creating backdoors on compromised systems. This is accomplished by searching for vulnerabilities in the network such as unused accounts which have passwords that are easy to crack. Once the intruder is in they change the password to a different password that is difficult to break.
Why do hackers use backdoors?
Hackers use backdoors as a means of gaining repeated access to a network without being logged by the systems administrator. This type of network intrusion hides its presence while the hacker is actually using the network without the knowledge of others.
What is system privileges?
It allows you to change passwords and privileges for other accounts and basically have full access to the network and its components. There are many different types of backdoors but the type that allows the hacker full access is the most hazardous. ...
How to detect vulnerabilities in a network?
Vulnerabilities in a network system can be detected by using specialized software that the hacker activates from a remote location to sniff around the system and identify the weaknesses. The typical target is unused accounts or services or even accounts that have been disabled.
How to create a backdoor on a network?
In order to create a backdoor on a network the hacker must find the weak points in the system. The weak points are known as vulnerabilities which are the perfect location for an exploit. Often these are unused accounts on a network perhaps once used by a former employee that left the company or other type of situation.
What happens when an intruder changes the password?
When the systems administrator monitors the network, the account where the hacker modified the password does not appear. This makes it difficult to determine which accounts are unused and should be locked from the network.
What is a backdoor?
A backdoor is used by hackers to install malware for the purpose of stealing information from a network such as company trade secrets or customer financial data . Backdoors can also be used to launch Denial of Service attacks which can bring down an entire company network.
