Hackers have several ways of exploiting the vulnerabilities of remote access software in hopes of causing a security incident to a private network or system. If there’s a poor protocol for installing remote access software, then there’s a high chance for hackers to gain unwanted access to your system.
Full Answer
How to stop remote hacking?
- Educate your employees. Like most things in life, it all begins with education. ...
- Make VPNs mandatory. A virtual private network, or VPN, establishes a protected connection even when you’re using a public network.
- Use shared documents. ...
- Implement two-factor authentication. ...
- Teach staff how to recognise hacking attempts. ...
- Enforce regular password changes. ...
How to block remote hackers?
Steps
- Follow forums. It is always a good idea to follow hacking forums as you will be able to pick up on all the latest methods being used.
- Change default passwords immediately. Some software has built-in passwords to allow the first login after installation; it is extremely unwise to leave it unchanged.
- Identify entry points. ...
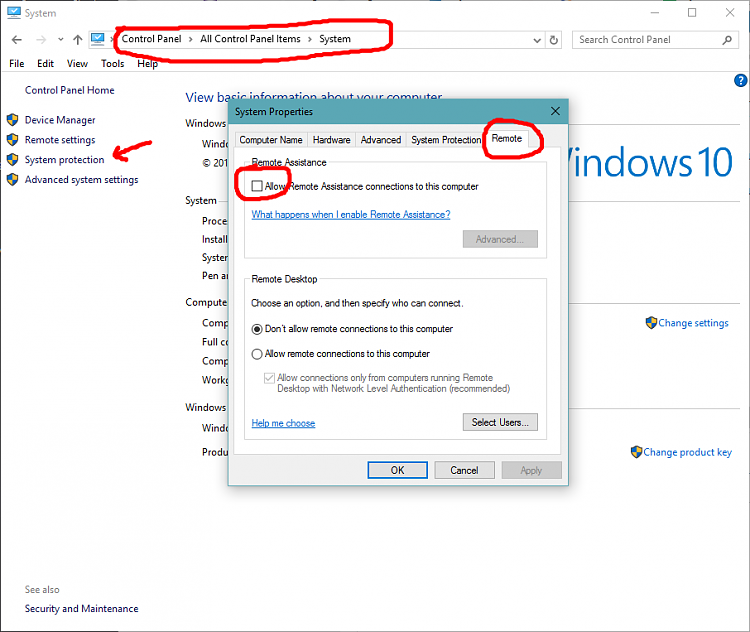
How can I prevent remote access to my Windows PC?
Windows 8 and 7 Instructions
- Click the Start button and then Control Panel.
- Open System and Security.
- Choose System in the right panel.
- Select Remote Settings from the left pane to open the System Properties dialog box for the Remote tab.
- Click Don’t Allow Connections to This Computer and then click OK.
What is the best remote access for PC?
What is the Best Remote Desktop Software?
- GoToMyPC. GoToMyPC is the best remote desktop software on this list. ...
- AnyDesk. AnyDesk is one of the most popular remote desktop software platforms, used by over 100 million users globally.
- LogMeIn. ...
- Parallels. ...
- Splashtop Business Access. ...
- Zoho Assist. ...
- ConnectWise Control. ...
- RemotePC. ...
- TeamViewer. ...
- Remote Utilities for Windows. ...

Can remote access be hacked?
Remote Desktop Protocol (RDP) has been known since 2016 as a way to attack some computers and networks. Malicious cyber actors, hackers, have developed methods of identifying and exploiting vulnerable RDP sessions via the Internet to steal identities, login credentials and install and launch ransomeware attacks.
What can hackers do remotely?
And in fact, no industry is safe from remote hackers.4 Common Types of Remote Attacks. ... Domain Name System (DNS) Poisoning. ... Port Scanning. ... Password Spraying. ... Phishing. ... Virtual Private Network (VPN) Attacks. ... Remote Desktop Protocol (RDP) Hacks. ... Remote Access Trojans (RAT)
How do hackers hack remotely?
Remote hackers use various malware deployment methods; the most common (and probably the easiest) way for hackers to reach unsuspecting victims is through phishing campaigns. In this scenario, hackers will send emails with links or files, which unsuspecting recipients may click on.
Can someone access my phone remotely?
Some spy apps are pretty easy to get hold of and can be used by a person without advanced IT knowledge. This lets them remotely monitor your phone activities. A person can install such an app by getting a direct access to your mobile device; A USB cable or charger lead could be used to hack your device.
Can hackers see you through your phone camera?
On top of that, popular app developers aren't immune to accusations of watching you through your phone's camera. Generally, however, a stalker would need to install spyware on your device in order to compromise it. Hackers can gain access to your phone physically, through apps, media files, and even emojis.
What do I dial to see if my phone has been hacked?
Use the code *#21# to see if hackers track your phone with malicious intent. You can also use this code to verify if your calls, messages, or other data are being diverted. It also shows your diverted information's status and the number to which the information is transferred.
Can cell phones be hacked remotely?
Yes. Unfortunately, they can even hack a phone's camera. But you can also learn how to block hackers from your Android or iOS phone.
Can someone hack my phone by texting me?
Android phones can get infected by merely receiving a picture via text message, according to research published Monday. This is likely the biggest smartphone flaw ever discovered.
Can hackers hack without internet?
Can an Offline Computer be Hacked? Technically — as of right now — the answer is no. If you never connect your computer, you are 100 percent safe from hackers on the internet. There is no way someone can hack and retrieve, alter or monitor information without physical access.
How do I block my phone from being monitored?
Turn off the cellular and Wi-Fi radios on your phone. The easiest way to accomplish this task is to turn on the “Airplane Mode” feature. This shuts down both your cell radios as well as the Wi-Fi radio installed inside your phone so that neither of them can connect to their respective networks.
How can you tell if your phone is being monitored by someone else?
Here are 10 of the most common signs that someone is spying on your phone:Unfamiliar Applications. ... Your Device is 'Rooted' or 'Jailbroken' ... The Battery Is Draining Fast. ... Your Phone Is Getting Very Hot. ... Unusually High Data Usage. ... Strange Activity In Standby Mode. ... Issues With Shutting Down the Phone. ... Odd SMS Messages.More items...•
Can you tell if someone is monitoring your cell phone?
Flashing of a blue or red screen, automated settings, unresponsive device, etc. could be some signs that you can keep a check on. Background noise while making calls - Some of the spying apps can record the calls made on the phone. To be sure, listen carefully while making a call.
Can hackers hack without internet?
Can an Offline Computer be Hacked? Technically — as of right now — the answer is no. If you never connect your computer, you are 100 percent safe from hackers on the internet. There is no way someone can hack and retrieve, alter or monitor information without physical access.
Can hackers hack your WIFI?
Hackers can hack your router, spy on your Wi-Fi connection and even eavesdrop on your conversations to steal personal information such as credit card details, passwords to your social media accounts, and even compromise your online banking apps.
Can someone hack my phone by texting me?
Android phones can get infected by merely receiving a picture via text message, according to research published Monday. This is likely the biggest smartphone flaw ever discovered.
What is the lesson to be learned from a year of remote access abuse?
If there’s a lesson to be learned from a year of remote access abuse, it’s that visibility remains the single biggest challenge. Although the ideal solution is to manage all remote access through a single, global service edge that combines networking and security, there are some steps organizations should take immediately to secure themselves. Like defense in depth, a multi-layered, remote-access, security approach that provides redundant layers of inspection and enforcement.
Where can forensic data be obtained?
Forensic data can only be obtained from the internet service provider or with the user’s consent. Attacks that leverage multiple, chained exploits can require retrieving logs from the cloud provider, the endpoint owner, the ISP – and then correlating all of that with any data the organization actually owns.
Is Microsoft Remote Desktop Protocol encrypted?
Even for those organizations that connect back to headquarters, most traffic is encrypted and uninspected. Microsoft Remote Desktop Protocol (RDP), Secure Shell (SSH) and Virtual Network Computing (VNC) remain popular, along with a host of open source VPNs. Most organizations rely heavily on personally owned devices, ...
Is cyber security a game?
Cybersecurity is a constant game of cat and mouse, with attackers and defenders locked in a perpetual race for finding, exploiting and patching vulnerabilities. With most of the world still working remotely, and by all indications looking to stay that way for the foreseeable future, it’s no surprise that attackers have locked onto compromising ...
Can an unmanaged device access corporate networks?
When you factor in the number of ways an unmanaged device can access corporate networks – direct to application, tunneling protocols and VPN – you can see how attacker dwell time can easily swell into the better part of a year undetected. Most personally owned devices have lax or nonexistent security controls compared to corporate devices.
How Can Someone Hack My Phone Remotely?
It's not a secret that hackers don't need to have your phone in their hands to steal your personal information. They can target any of the data stored there remotely. Passwords, SSNs, bank account details, text messages, photos—almost anything can get into the hands of the bad guys if you aren't careful enough and well-protected.
What are some ways hackers can get access to your phone?
Cybercriminals create fake Wi-Fi networks, and when you connect to it with your phone, they redirect you to malicious sites. SIM swaps. Hackers transfer your phone number to their device and gain access to your account. Phishing emails or texts.
How to reset a phone?
If you don't want to run a factory reset on your smartphone, there are some other things that you can try: 1 Get rid of suspicious apps. Search for applications that you haven't installed by yourself on your phone and delete them. However, there are no guarantees that this will help for sure. 2 Install an antivirus application. It can detect any malicious software or processes on your device and help you protect your smartphone from future possible hacker attacks. 3 Tell your contacts that you've been hacked. It's best to let them know that they shouldn't open any suspicious messages coming from your phone number so that they won't get into any trouble.
What is phishing email?
Phishing emails or texts. Hackers send you an email with a malicious link and try to trick you into clicking it. Such emails or texts may look very real, and sometimes it may be complicated to distinguish between a malicious site and a legitimate one.
How to prevent your phone from getting hacked?
Make sure that your device and the apps installed on it are up-to-date. Don't jailbreak your phone. This can increase the chances of your smartphone getting hacked later on. Use two-factor authentication. An extra layer of security for your apps will ensure that you're the only one who can access them.
Why turn off hotspot?
Turn off your hotspot in crowded places. It makes it easier for the hacker to get access to your device when it is turned on. And if you're using this feature, then make sure you have a strong password set.
How to prevent malware from using your phone?
If your phone also has such features as Touch ID or Face ID, then set it up as well. Don't turn on mobile data or Wi-Fi unless you need to use them. This can prevent malicious software from using your data.
Why is remote access important?
Remote access is a great feature for certain industries and employers, because it helps to connect employees to necessary servers and storage devices via their internet connection. Beyond workplace settings, however, there are limited cases in which you would want to access your device remotely.
How to check if someone accessed my PC?
Another option is to check the Windows Event Viewer app to look for any unfamiliar remote access. This app shows a log of application use and system messages, including error messages, with timestamps. If you don’t recognize a particular action at a time that you were on your device, then it is likely that someone accessed your PC. You can find this app in the Windows search bar by searching for "Event Viewer."
How often do hackers attack people?
There is no doubt that hacking and cybercrime are on the rise. In fact, it is estimated that hackers attack someone online every 32 seconds. While many of them target companies and organizations, others go after private individuals in an attempt to steal personal information from computers, cell phones, and tablets.
How to stay ahead of hackers?
You can stay ahead of hackers by keeping an eye on your online accounts to see if there are any recent changes. It’s easy to overlook this step, especially if you don’t use a particular account often or you don’t look at your own page frequently, in Facebook for example.
How to prevent identity theft?
Also, disconnect any credit cards or other financial information tied to your account settings. This will help prevent further identity theft and ensure that your sensitive data does not fall into the wrong hands.
How to know if someone logged into my account?
Most major online accounts will allow you to see when someone has logged into your account and from what location or IP address (click here to learn how to find your IP address). If you do not recognize the login attempt, then you should immediately change your password and notify the company that your account was compromised.
What to do if you fall victim to a Trojan attack?
If you fall victim to a Trojan attack, there are steps you can take to mitigate it. First, you need to format your hard drive, which may be painful if you haven’t backed up your important data. For those who may not be up to date with this critical maintenance task, check out our list of the best Windows backup softwareto be prepared.
What are remote hackers?
With the rise of a remote working population, “remote hackers” have been re-emerging as well. These remote hackers take advantage of remote working technologies like video conferencing tools, enterprise VPNs, and other remote access solutions that have become popular during the COVID-19 crisis.
How do remote hackers reach unsuspecting victims?
Remote hackers use various malware deployment methods; the most common (and probably the easiest) way for hackers to reach unsuspecting victims is through phishing campaigns.
What are hackers exploiting?
While hackers are exploiting the vulnerabilities found in actual solutions like business VPNs and RDP to gain access to the company network, they are using traditional tactics to target remote employees.
Why do VPNs run 24/7?
VPNs run 24/7, which means organizations are less likely to check for and apply security patches on a regular basis. This also makes VPNs vulnerable and susceptible to attacks by hackers. For instance, hackers may start a phishing campaign to target remote employees in order to steal their usernames and passwords that gives them access to the VPN, and by extension, your network.
Can malware be executed on a client?
The malware is then executed within the client — the victim’s device; the compromised device is left open to the hackers so they can access the private network directly. Hackers may also try to instill the use of macros within Excel or Word docs to execute malware and take over a PC.
Can hackers steal your credentials?
Hackers with stolen credentials in hand (acquired through brute force or other malicious ways) may exploit this port to gain access to the internal network of a company or organization. Just as hackers can steal the login credentials for corporate VPNs , hackers can also acquire the ID/PWs of RDP users too.
