Remote access Trojan (RAT) programs are malware programs that allow the target computer to be controlled remotely. A user may download RATs invisibly with a program they request — such as a game — or send them as an email attachment. Keylogging or other spyware can be used to monitor user behavior.
Full Answer
What can a Remote Access Trojan do?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Can remote access Trojans be detected?
As you might imagine, this can lead to sticky situations. A Remote Access Trojan paired with a keylogger, for instance, can easily acquire login information for bank and credit card accounts.
What is the best Remote Access Trojan?
What is Remote Access and Administration?...10 Best Remote Access Software (Remote Control Software) In 2022Comparison of Top Remote Access Tools.#1) NinjaOne (Formerly NinjaRMM)#2) SolarWinds Dameware Remote Support.#3) Atera.#4) Supremo.#5) ManageEngine Remote Access Plus.#6) RemotePC.#7) TeamViewer.More items...•
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
How do I know if someone is accessing my computer remotely?
You can try any of these for confirmation.Way 1: Disconnect Your Computer From the Internet.Way 2. ... Way 3: Check Your Browser History on The Computer.Way 4: Check Recently Modified Files.Way 5: Check Your computer's Login Events.Way 6: Use the Task Manager to Detect Remote Access.Way 7: Check Your Firewall Settings.More items...•
Can an Iphone get a Remote Access Trojan?
The only way to get a Remote Access Trojan on an iOS device would be to jailbreak it to remove the inherent iOS limitations of file system and app sandboxes and to open restricted ports (that are blocked by iOS itself by default).
What is smart RAT switch?
RAT infected Android devices can be remotely zombified by the perpetrator, allowing virtually unlimited access to photos, data and messages on the device. The Dendroid RAT provides full access to infected devices' camera and microphone, and can place calls or listen in on a user's phone conversations or text messages.
Can Remotepc be hacked?
Remote Desktop Protocol (RDP) has been known since 2016 as a way to attack some computers and networks. Malicious cyber actors, hackers, have developed methods of identifying and exploiting vulnerable RDP sessions via the Internet to steal identities, login credentials and install and launch ransomeware attacks.
What is a remote access tool?
Remote access programs and tools (sometimes referred to as RATs) allow access and manipulation of systems remotely from another location. Many remote access programs are legitimate tools used by all types of users to access files and data on remote computers.
What is a backdoor Trojan?
Backdoor malware is generally classified as a Trojan. A Trojan is a malicious computer program pretending to be something it's not for the purposes of delivering malware, stealing data, or opening up a backdoor on your system.
Can you get a RAT on your phone?
RATs in Your Android It's well documented, freely available, and gives an attacker complete control over infected devices. There are even tutorials on how to use the RAT, and free, easy-to-use tools that will inject its malicious code into legitimate apps.
What was the first remote access Trojan?
The oldest RAT was first developed in 1996 [10], however legitimate remote access tools were first created in 1989 [11]. Since then, the number of RATs has grown rapidly. The first phase was marked by home-made RATs. In these years, everyone made their own RAT, however these did not prosper and were not heavily used.
Can Norton detect RATs?
Antivirus software like Bitdefender, Kaspersky, Webroot, or Norton, can detect RATs and other types of malware if they infect your devices.
Can MalwareBytes remove RATs?
SolarWinds Security Event Manager (FREE TRIAL) provides advanced threat protection against some of the most persistent RATs on the web. SEM can even take automated action to clean and remove any RATs found on infected computers. MalwareBytes Anti-Malware can remove most of some of the most common threats found online.
What is smart RAT switch?
RAT infected Android devices can be remotely zombified by the perpetrator, allowing virtually unlimited access to photos, data and messages on the device. The Dendroid RAT provides full access to infected devices' camera and microphone, and can place calls or listen in on a user's phone conversations or text messages.
What can we do in order to limit or prevent remote access?
Firewalls can be your first line of defense in network security by limiting those who have remote access. You should set up firewalls to restrict access using software or hardware or both. Update your software regularly. Make sure your software updates automatically so you're working with the latest security fixes.
What is RAT software?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can ac...
What’s the difference between the RAT computer virus and RAT software?
As for functions, there is no difference between the two. Yet, while remote administration tool is for legit usage, RAT connotes malicious and crim...
What are the popular remote access applications?
The common remote desktop tools include but are not limited to TeamViewer, AnyDesk, Chrome Remote Desktop, ConnectWise Control, Splashtop Business...
How to protect yourself from remote access trojans?
Just like protecting yourself from other network malware threats, for remote access trojan protection, in general, you need to avoid downloading unknown items; keep antimalware and firewall up to date, change your usernames and passwords regularly; (for administrative perspective) block unused ports, turn off unused services, and monitor outgoing traffic.
What is a RAT trojan?
RAT trojan is typically installed on a computer without its owner’s knowledge and often as a trojan horse or payload. For example, it is usually downloaded invisibly with an email attachment, torrent files, weblinks, or a user-desired program like a game. While targeted attacks by a motivated attacker may deceive desired targets into installing RAT ...
What Does a RAT Virus Do?
Since a remote access trojan enables administrative control , it is able to do almost everything on the victim machine.
How does RAT malware work?
Once get into the victim’s machine, RAT malware will hide its harmful operations from either the victim or the antivirus or firewall and use the infected host to spread itself to other vulnerable computers to build a botnet.
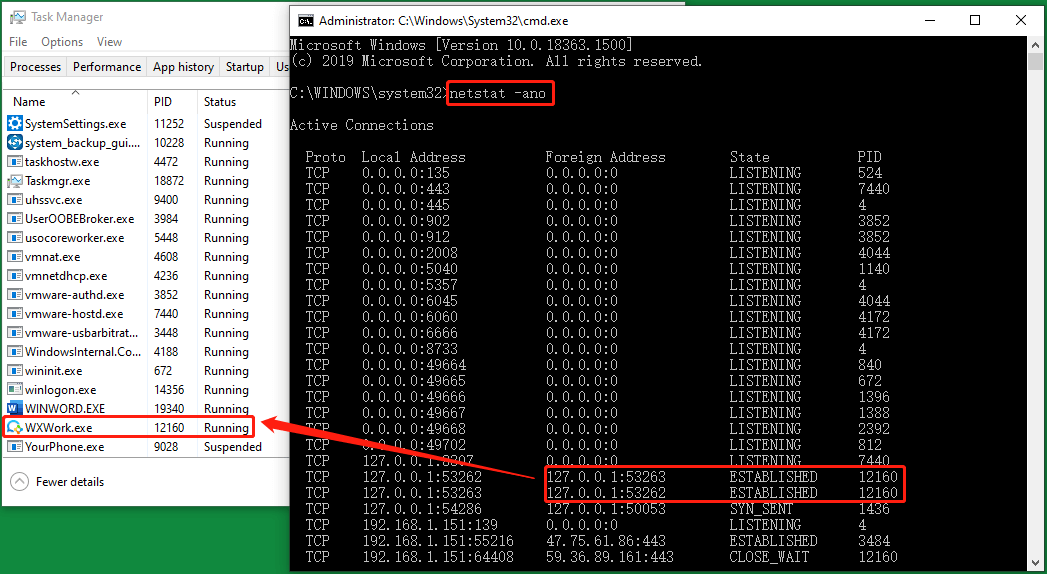
Why do RATs use a randomized filename?
It is kind of difficult. RATs are covert by nature and may make use of a randomized filename or file path structure to try to prevent identification of itself. Commonly, a RAT worm virus does not show up in the lists of running programs or tasks and its actions are similar to those of legal programs.
Is Sub 7 a trojan horse?
Typically, Sub 7 allows undetected and unauthorized access. So, it is usually regarded as a trojan horse by the security industry. Sub7 worked on the Windows 9x and Windows NT family of OSes, up to and including Windows 8.1. Sub7 has not been maintained since 2014. 4.
Can a RAT remote access trojan be used on a computer?
Since RAT remote access trojan will probably utilize the legitimate apps on your computer, you’d better upgrade those apps to their latest versions. Those programs include your browsers, chat apps, games, email servers, video/audio/photo/screenshot tools, work applications…
How Does A Remote Access Trojan Work?
A Remote Access Trojan (RAT) infects a computer with a virus that gives cyberattackers unrestricted access to the data on the PC by using the victim’s access permissions. A RAT can include backdoors into the computer system, which can be used to create a botnet and spread to other devices as well.
What Is The Use Of Remote Access Trojan?
Malware developers use Remote Access Trojan (RAT) tools to gain full access and control over a user’s computer, including mouse and keyboard control, file access, and network resources.
What Damage Can A Trojan Do?
In general, a Trojan is designed to damage, disrupt, steal, or in general cause some other harm to your data or network. You are fooled by a Trojan by pretending to be a legitimate application or file.
What Is The Best Trojan Remote Access?
Hackers commonly use Blackshades to gain remote access to computers. Windows-based operating systems are frequently targeted by this tool. The Trojan has infected 500,000 systems worldwide until now.
What Is The Purpose Of A Trojan Horse?
In general, a Trojan is designed to damage, disrupt, steal, or in general cause some other harm to your data or network.
What Is Trojan Ddos?
An infected computer is used to launch a DoS attack from a pre-defined address using this type of malicious program. The malicious user infects a number of computers with this type of Trojan in advance (for example, as part of a mass spam mailing) in order to conduct a successful DoS attack.
Is Remote Access Detectable?
Could the website detect that Desktop 2 is being remotely operated? Desktop 1 cannot be detected, but remote operations can be. There is no way they can do it. In theory, if they have access to your home ISP, they could see the inbound/outbound connections between your home PC and the server.
How do remote access Trojans work?
The Remote Access Trojans get themselves downloaded on a device if the victims click on any attachment in an email or from a game. It enables the attacker to get control over the device and monitor the activities or gaining remote access. This RAT makes itself undetected on the device, and they remain in the device for a longer period of time for getting data that may be confidential.
What is the most powerful Trojan?
One of the most powerful Trojans that are popularly used by the attacker or hacker is Remote Access Trojan. This is mostly used for malicious purposes. This Trojan ensures the stealthy way of accumulating data by making itself undetected. Now, these Trojans have the capacity to perform various functions that damages the victim.
What is the advantage of remote access?
Advantage of Remote Access Trojans : It can be used to capture screenshots. The attacker can activate the webcam, or they can record video. The RAT can be used to delete the files or alter files in the system. It can also be used to capture screenshots.
Can an attacker record video?
The attacker can activate the webcam, or they can record video.
What is a RAT?
"RAT" is an acronym for remote access trojan. A RAT is as the name implies; It is a trojan that allows a hacker to have remote access to your computer. Many popular RAT generators allow you to quickly create an executable file. Imagine some malicious person sends the .exe file to someone and says, "I cracked this online game. Play it with me!".
How do I get a RAT?
A RAT could be found everywhere. A RAT can be turned into a virus so it spreads easily to your friend's computer. A RAT can achieve this by modifying other files on your computer which you might send to other people. The same can be said with unknowingly infected friends sending one to you.
How do I remove a RAT?
There is usually very little you can do to get rid of a RAT from your computer. If the RAT was created using a popular tool like Nanocore, you might be able to search on Google for a removal tool. Determining what the RAT was made with can be difficult and even a waste of your time. Using a RAT removal tool, in general, may be a waste of your time.
Mitigating the risk of downloading a RAT
To best avoid downloading a RAT, you need to trust no-one. Only download content from big-time companies. Understand that any rogue teenager could create a fake website, fake emails, and malicious software like apps or bots. Anyone can achieve a high Google search result too. Relying on an anti-virus is not the smartest decision.
How do I know if I have a RAT?
A RAT can be incredibly difficult to spot if used by the hacker correctly.
Do not use this article for bad
I pretty much gave enough information to let you know how to make a RAT with Nanocore. If you want to experiment, please only test Nanocore on your spare computers. In doing so, you can better understand the potential and dangers of a RAT. Please do not use a RAT generator for malicious purposes.
Summary
A remote access trojan is a type of malware that allows a hacker to get full control of a computer through the internet. A RAT allows the hacker to view the webcam, control the keyboard and mouse, and download files.
What Is a Remote-Access Trojan?
A RAT is a piece of software that gives a stranger the ability to watch anything you do on a device. That stranger can also do anything on your device you're able to do.
Why do hackers use RAT malware?
Every hacker is different, and they all enter the work with different goals and objectives. But in general, people use a tool like this for a few specific purposes.
How are Remote Access Trojans Useful to Hackers?
Attackers using remote control malware cut power to 80,000 people by remotely accessing a computer authenticated into SCADA (supervisor y control and data acquisition) machines that controlled the country’s utility infrastructure. RAT software made it possible for the attacker to access sensitive resources through bypassing the authenticated user's elevated privileges on the network. Having access to critical machines that control city resources and infrastructure is one of the biggest dangers of RAT malware.
Why do attackers use remote devices?
Instead of storing the content on their own servers and cloud devices, attackers use targeted stolen devices so that they can avoid having accounts and servers shut down for illegal content.
How to install a RAT?
An attacker must convince the user to install a RAT either by downloading malicious software from the web or running an executable from a malicious email attachment or message. RATs can also be installed using macros in Microsoft Word or Excel documents. When a user allows the macro to run on a device, the macro silently downloads RAT malware and installs it. With the RAT installed, an attacker can now remotely control the desktop, including mouse movement, mouse clicks, camera controls, keyboard actions, and any configured peripherals.
What is remote control software?
Legitimate remote-control software exists to enable an administrator to control a device remotely. For example, administrators use Remote Desktop Protocol (RDP) configured on a Windows server to remotely manage a system physically located at another site such as a data center. Physical access to the data center isn’t available to administrators, so RDP gives them access to configure the server and manage it for corporate productivity.
What happens if you remove the internet from your computer?
Removing the Internet connection from the device disables remote access to your system by an attacker. After the device can no longer connect to the Internet, use your installed anti-malware program to remove it from local storage and memory. Unless you have monitoring configured on your computer, you won't know which data and files transferred to an attacker. You should always change passwords across all accounts, especially financial accounts, after removing malware from your system.
Why do attackers use RATs?
RATs have the same remote-control functionality as RDPs, but are used for malicious purposes. Attackers always code software to avoid detection, but attackers who use a RAT risk being caught when the user is in front of the device and the mouse moves across the screen. Therefore, RAT authors must create a hidden program and use it when the user is not in front of the device. To avoid detection, a RAT author will hide the program from view in Task Manager, a Windows tool that lists all the programs and processes running in memory. Attackers aim to stay hidden from detection because it gives them more time to extract data and explore network resources for critical components that could be used in future attacks.