Full Answer
What is a remote access trojan (RAT)?
What is a Remote Access Trojan (RAT)? Malware developers code their software for a specific purpose, but to gain remote control of a user’s device is the ultimate benefit for an attacker who wants to steal data or take over a user’s computer.
Can Android banking Trojans use accessibility services?
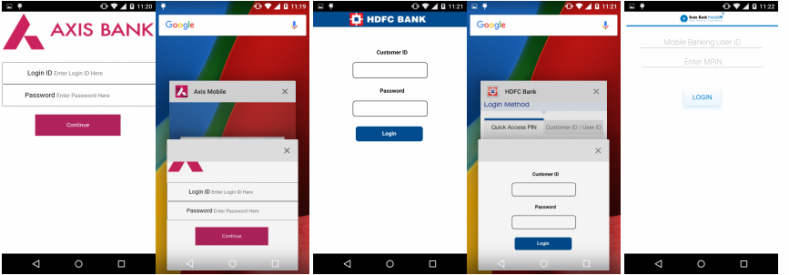
While it is not unusual for Android banking Trojans to leverage the Accessibility Services to conduct nefarious operations, they usually employ HTML overlays to trick users into revealing their login credentials. Vultur does employ overlay to gain access to all of the permissions it needs to run unhindered on the compromised device.
What are banking trojans and how dangerous are they?
Unfortunately for the average person, banking trojans are extremely sophisticated and frequently switch up their strategies. They can attack online banking institutions, and even drain money from personal or business bank accounts— before the account owner knows they’ve been targeted. How do banking trojans work?
What is the Vultur Android banking trojan?
Masquerading as an application called Protection Guard, Vultur is projecting the screen, an operation visible in the notification panel. While it is not unusual for Android banking Trojans to leverage the Accessibility Services to conduct nefarious operations, they usually employ HTML overlays to trick users into revealing their login credentials.

What is banking Trojan?
The term banking Trojan indicates a category of malware that aims to steal the banking credentials of victims and carry out online fraud, usually causing significant economic damage.
What does a remote access Trojan do?
Remote access trojans (RATs) are malware designed to allow an attacker to remotely control an infected computer. Once the RAT is running on a compromised system, the attacker can send commands to it and receive data back in response.
Can remote access Trojans be detected?
AIDE—short for Advanced Intrusion Detection Environment—is a HIDS designed specifically to focus on rootkit detection and file signature comparisons, both of which are incredibly useful for detecting APTs like Remote Access Trojans.
How is remote access Trojan delivered?
A remote access Trojan (RAT) is a malware program that includes a back door for administrative control over the target computer. RATs are usually downloaded invisibly with a user-requested program -- such as a game -- or sent as an email attachment.
Is someone using my computer remotely?
Open your Task Manager or Activity Monitor. These utilities can help you determine what is currently running on your computer. Windows – Press Ctrl + Shift + Esc. Mac – Open the Applications folder in Finder, double-click the Utilities folder, and then double-click Activity Monitor.
How can I find a hidden virus on my computer?
You can also head to Settings > Update & Security > Windows Security > Open Windows Security on Windows 10, or Settings > Privacy and Security > Windows Security > Open Windows Security on Windows 11. To perform an anti-malware scan, click “Virus & threat protection.” Click “Quick Scan” to scan your system for malware.
What is smart RAT switch?
RAT infected Android devices can be remotely zombified by the perpetrator, allowing virtually unlimited access to photos, data and messages on the device. The Dendroid RAT provides full access to infected devices' camera and microphone, and can place calls or listen in on a user's phone conversations or text messages.
What was the first remote access Trojan?
The oldest RAT was first developed in 1996 [10], however legitimate remote access tools were first created in 1989 [11]. Since then, the number of RATs has grown rapidly. The first phase was marked by home-made RATs. In these years, everyone made their own RAT, however these did not prosper and were not heavily used.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
What is a Remote Access Trojan which is installed by SMS spoofing used for?
Remote Access Trojans are programs that provide the capability to allow covert surveillance or the ability to gain unauthorized access to a victim PC.
What are RAT files?
(peshkov) A Remote Access Trojan, otherwise known as a RAT, is a type of spyware that allows a cybercriminal to take control of the computer or other device it's installed on. RATs are malicious software that constitute a major cybersecurity threat.
Which connection is most commonly used in RATs?
RAT infections are typically carried out via spear phishing and social engineering attacks. Most are hidden inside heavily packed binaries that are dropped in the later stages of the malware's payload execution.
What is a backdoor in cyber security?
Definition(s): An undocumented way of gaining access to computer system. A backdoor is a potential security risk.
What was the first remote access Trojan?
The oldest RAT was first developed in 1996 [10], however legitimate remote access tools were first created in 1989 [11]. Since then, the number of RATs has grown rapidly. The first phase was marked by home-made RATs. In these years, everyone made their own RAT, however these did not prosper and were not heavily used.
Which of the following is a remote Trojan?
Troya is a remote Trojan that works remotely for its creator.
What are the common backdoor?
7 most common application backdoorsShadowPad. ... Back Orifice. ... Android APK backdoor. ... Borland/Inprise InterBase backdoor. ... Malicious chrome and Edge extension backdoor. ... Backdoors in outdated WordPress plugins. ... Bootstrap-Sass Ruby library backdoor.
What is RAT software?
RAT can also stand for remote administration tool, which is software giving a user full control of a tech device remotely. With it, the user can ac...
What’s the difference between the RAT computer virus and RAT software?
As for functions, there is no difference between the two. Yet, while remote administration tool is for legit usage, RAT connotes malicious and crim...
What are the popular remote access applications?
The common remote desktop tools include but are not limited to TeamViewer, AnyDesk, Chrome Remote Desktop, ConnectWise Control, Splashtop Business...
How to protect yourself from remote access trojans?
Just like protecting yourself from other network malware threats, for remote access trojan protection, in general, you need to avoid downloading unknown items; keep antimalware and firewall up to date, change your usernames and passwords regularly; (for administrative perspective) block unused ports, turn off unused services, and monitor outgoing traffic.
What is a RAT trojan?
RAT trojan is typically installed on a computer without its owner’s knowledge and often as a trojan horse or payload. For example, it is usually downloaded invisibly with an email attachment, torrent files, weblinks, or a user-desired program like a game. While targeted attacks by a motivated attacker may deceive desired targets into installing RAT ...
What Does a RAT Virus Do?
Since a remote access trojan enables administrative control , it is able to do almost everything on the victim machine.
How does RAT malware work?
Once get into the victim’s machine, RAT malware will hide its harmful operations from either the victim or the antivirus or firewall and use the infected host to spread itself to other vulnerable computers to build a botnet.
Why do RATs use a randomized filename?
It is kind of difficult. RATs are covert by nature and may make use of a randomized filename or file path structure to try to prevent identification of itself. Commonly, a RAT worm virus does not show up in the lists of running programs or tasks and its actions are similar to those of legal programs.
Is Sub 7 a trojan horse?
Typically, Sub 7 allows undetected and unauthorized access. So, it is usually regarded as a trojan horse by the security industry. Sub7 worked on the Windows 9x and Windows NT family of OSes, up to and including Windows 8.1. Sub7 has not been maintained since 2014. 4.
Can a RAT remote access trojan be used on a computer?
Since RAT remote access trojan will probably utilize the legitimate apps on your computer, you’d better upgrade those apps to their latest versions. Those programs include your browsers, chat apps, games, email servers, video/audio/photo/screenshot tools, work applications…
