What is secure remote access?
Secure Remote Access is a combination of security processes or solutions that are designed to prevent unauthorized access to an organization's digital assets and prevent the loss of sensitive data.
How do you secure remote privileged access to third party technicians?
Best Practices for Third-Party Vendor Remote AccessIdentify users.Audit all high-risk access points.Implement and enforce vendor remote access policies.Apply access controls.Monitor user access.Automate vendor remote access.
Which method of remote access is the most secure?
Implement a Secure Connection for Remote Network AccessWired Connection: A wired connection is the most secure method for remote network access.Home Wi-Fi: The second most secure network connection is using a secured home Wi-Fi connection.More items...•
What are third party connections?
Third Party Connection A direct connection to a party external to the Board. Examples of third party connections include connections to customers, vendors, partners, or suppliers.
What is BeyondTrust remote?
BeyondTrust Remote Support Software enables support organizations to access and support nearly any remote computer or mobile device. Troubleshoot PCs and servers, provide remote assistance, train remote employees, or perform system maintenance . . . all with the highest levels of security.
What is beyond trust remote client?
The BeyondTrust Customer Client enables customers to interact with representatives during remote support, chat or presentation sessions. Because it is the most secure remote support solution, BeyondTrust places a top priority on user controls.
Who is more secure protocol for remote login?
Virtual private networks (VPNs) are a commonly used remote-access solution. They are designed to provide an encrypted tunnel for network traffic between a remote user and the enterprise network. VPNs also support security solutions like MFA that help to mitigate the threat of compromised accounts.
What are the two types of remote access servers?
Remote Access Methods1- Remote Access Server: It's one server in organization network that it is the destination of all remote access connections.2- Remote Access Client: All computers that remote connect to network, called remote access client or remote computer.More items...•
How do I protect my remote connection?
Use strong passwords One way of initiating security for your remote desktop connection is by generating a strong password. This will serve as the first line of defense of your organization's RDP against any unwanted attacks and threats.
What is third party VPN?
Third-party VPN services work by installing software, a browser plugin or a security hardware appliance between end devices and the internet. A VPN tunnel is then established between the end-user device and the service provider's VPN endpoint on the internet.
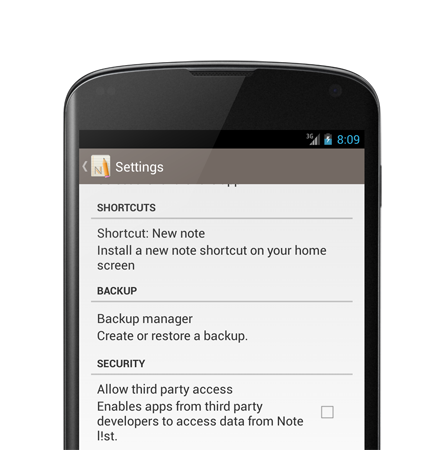
How can you tell if a app is third party?
Review what a third party can access Go to the Security section of your Google Account. Under “Third-party apps with account access,” select Manage third-party access. Select the app or service you want to review.
What is third party access policy?
Third-party access refers to the process of an organization granting external vendors and service providers secure access to corporate IT assets for maintenance, administration and management purposes.
What are the remote access methods?
The primary remote access protocols in use today are the Serial Line Internet Protocol (SLIP), Point-to-Point Protocol (PPP), Point-to-Point Protocol over Ethernet (PPPoE), Point-to-Point Tunneling Protocol (PPTP), Remote Access Services (RAS), and Remote Desktop Protocol (RDP).
What are three examples of remote access locations?
What Is Remote Access?Queens College.Harvard University Extension School.
What is the technology used in remote access?
virtual private network (VPN) technologyRemote access software is usually accomplished using a virtual private network (VPN) technology. This type of method is more available compared to others since it is a more secure remote access software that connects the user and the enterprise's networks through an internet connection.
Why is remote authentication important?
MFA is important for remote workers for not only preventing unauthorized access, but in improving your organization's overall security posture. This is thanks to one of the great features of MFA: when an attempt is made to get into someone's account from an unauthorized device, the user will get a notification.
What is third party remote access?
Third-party remote access is the system in which external users are able to connect with a defined network. The best third-party remote access platform will make sure that the connection is secure, controlled, and monitored at all times. Sadly, many enterprises still give their third-party vendors VPN credentials that often provide privileged access. Frequently, this access is taken advantage of by bad actors because they can easily use a third-party vendor’s credentials to get onto an enterprise’s network.
Why do companies work with third party vendors?
Third-party vendors often provide specialized services that are more cost-effective. Since most third-party vendors work offsite, they need remote access to your network in order to support their technology. If you do not securely manage this third-party network access, your vulnerable surface area gets bigger. In other words, you’re leaving doors open that could lead to a breach of confidential data or a ransomware attack. It’s critical to have complete control over every vendor connection, tight credential management, and audit for all user activity.
How to protect your network from hackers?
Now is the time to get your vendors and platform aligned. Here are some next steps you should take: 1 Prepare for an attack from multiple vectors. A great place to start is to catalog the points of entry into your network and prioritize which present the greatest security vulnerability. Remember, threats can come both internally and externally. 2 Assess your current technology. Cybersecurity is a complex problem and technology alone will not secure your systems-internal training and process are also essential. However, when it comes to third-party remote access, the technology you select must protect against the vulnerabilities you outlined in attack preparation. It’s also important that your tech’s functionality is complementary to how your team works. 3 Create a realistic third-party access security policy. Protect your most valuable data by considering how it may be vulnerable and simple steps that can be taken to mitigate risk. Look at different options to protect your organization. As organizations continue to struggle over where responsibility lies and who is liable in the event of a data breach, taking a holistic approach is critical in protecting your organization.
What is Shodan's spike in remote desktop protocol?
From the onset of the Covid-19 outbreak until the end of March, Shodan (a global search engine that scans and indexes internet-connected devices) tracked a 41% spike in Remote Desktop Protocol...
Who is Tonya Ugoretz?
Tonya Ugoretz, deputy Assistant Director of the FBI...
Can We Really Make the World a Passwordless Place?
The average person uses around 100 username and password combinations. However, while many security teams recommend business users create individual, complex and strong passwords for all their...
What is managed service provider?
Your managed service providers (MSPs) provide critical IT services and support that allow your organization to run smoothly and effectively. With providing these services comes access to privileged accounts, systems, and data. Ensure that you can control that access, while always have visibility into what they are doing.
Do contractors need access to data?
Your contractors often need access to systems and data on your network to do the job you hired them for, but that can include privileged or sensitive information. Ensure they only have access to what they need and automatically deactivate their access once the contract is complete.
Do third parties need to know network credentials?
Ensure that those parties are also individually identified and never need to know network credentials for their access.
What is a third party service?
Third parties provide services like IT/IS, HR, software support, sales, and other related support and business operations services depending on the type of organization. Nonetheless, it does not matter the type of access it is; what matters is how the third-party access is managed, and how the business assures the access is secure. The organization must manage the risk from third-party activity.
What does reporting access do?
By reporting the access, the organization has visibility and can determine if the access is still required. For instance, if there has been no access for several months, an informed decision can be made regarding if the third-party access is still required going forward. Some organizations have policies in place to shut the access if it’s not used for 60 days, and this is made visible through reporting. The access can be reapproved when it’s requested again. By doing this, the attack surface area is reduced.
What is a matrix once access has been mapped?
Once the access has been mapped, a matrix can be created of who is accessing what from where and when (then links can be defined). At this point, consideration of systems that monitor access is undertaken to decide on an effective system to implement.
Why is it important to know who has access to what?
Through doing this, the organization has a reference point that can be used to audit. Making this start is vital to getting third-party access under control.
When can controls be put in place to manage the access accordingly?
Once the full picture is visible and understood , controls can be put in place to manage the access accordingly.
Is VPN or SSL/TLS security necessary?
Ensuring access to systems is secure from a network perspective is also essential. Using a VPN or SSL/TLS level security to the central point is a more secure way than not having this protection. Third parties do not always have the equivalent or better level of security that an organization may have, and by protecting the access through encrypted networks adds assurance. It’s not the only control needed; a combination of controls should be implemented to effectively mitigate the risk. Some organizations tend to go with one control or another; a combination is necessary.
What is Zscaler private access?
Zscaler Private Access is a ZTNA service that takes a user- and application-centric approach to network security. Whether a user is an employee, contractor, or third-party partner, ZPA ensures that only authorized users have access to specific internal applications without ever providing access to the network. Rather than relying on physical or virtual appliances, ZPA uses lightweight infrastructure-agnostic software, paired with browser access capabilities, to seamlessly connect all types of users to applications via inside-out connections that are stitched together within the Zscaler Security Cloud.
What is ZPA browser access?
With ZPA browser access service, third-party partners and users gain secure application access without the need for a client. Partners no longer need to jump through hoops to access enterprise applications—they simply use their own device to effortlessly access the apps over the internet. The outcome is highly controlled partner access that allows users to connect to private applications from any device, any location, and at any time.
What was visibility into partner activity before?
Before: With remote access solutions, visibility into partner activity was limited to IP address and port data.
Is it risky to extend full network access?
With increasingly dangerous security threats, it’s risky to extend full and lateral network access to your partners. But you do need to provide them with access to a subset of private applications. The solution is to be able to decouple application access from the network, while segmenting access based on individual users and apps, and the only way to achieve this is through zero trust network access (ZTNA) technology.
What is privileged credentials?
These should never be handed to vendors. Restricted controls are the only way to securely manage third-party remote access. While some third-parties may need privileged permissions to support their technology on an enterprise network, sweeping access should not be given. Ensure user accounts aren’t shared and every action is tied to an individual – helping ensure accountability and compliance.
What is the first step in two factor authentication?
The first step is making sure the user attempting to access your network is authorized and authenticated. Two-factor authentication should be baked into your access management systems. It demands two independent identity checks that will stifle intruders holding stolen passwords. You want the two factors to authenticate the identity of the user as well as confirm the user has authorized access. Requiring a simple username and password does neither of these.

Third-Party Remote Access Definition
- Third-party remote access is the system in which external users are able to connect with a defined network. The best third-party remote access platformwill make sure that the connection is secure, controlled, and monitored at all times. Sadly, many enterprises still give their third-party vendors credentials that often provide privileged access. Fr...
Third-Party Best Practices: Securing Your Access Points
- Now is the time to get your vendors and platform aligned. The best way to protect your most valuable assets and make sure your vendors stay safe in case of a breach is to practice critical access management. Made up of three pillars (access governance, access control, and access monitoring), employing the best techniques to practice third-party access management is the be…
Third-Party Access Control
- Access control, or having precision and control over when and how a person can exercise their access rights, can apply to both internal and external users. It’s especially important to apply types of access control to third parties, as they carry with them the biggest risk. Access control is an additional layer of security on top of access governance that helps protect those assets that …